The Encrypted Sandbox: Deconstructing the Homomorphic Encryption Market Platform
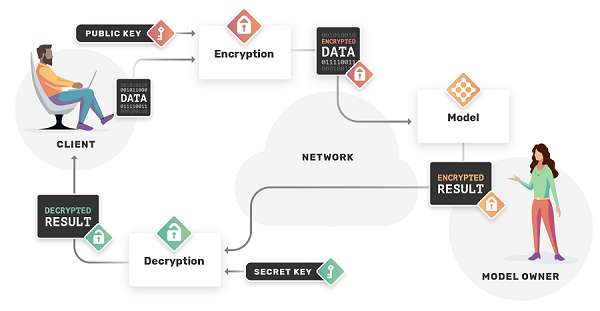
The groundbreaking capability of computing on encrypted data is enabled by a highly specialized and complex technological framework, which can be understood as the Homomorphic Encryption Market Platform. This is not a simple, off-the-shelf product but a sophisticated software stack designed to make the esoteric mathematics of homomorphic encryption accessible to developers and applicable to real-world problems. The architecture of this platform is centered around a core cryptographic library that implements the underlying HE scheme (e.g., BFV, CKKS, or TFHE). This library handles the complex operations of key generation, encryption, decryption, and, most importantly, the execution of homomorphic operations (like additions and multiplications) on the ciphertext. The platform then builds layers of abstraction on top of this core library to provide a more user-friendly and functional environment for building privacy-preserving applications. The ultimate goal is to create a platform where a developer, who is an expert in data science or application development but not in advanced cryptography, can leverage the power of homomorphic encryption without needing to understand the deep mathematical complexities that make it work.
The foundational layer of any homomorphic encryption platform is the core cryptographic library. This is where the deep mathematical research is translated into optimized C++ or other low-level code. Major open-source libraries like Microsoft's SEAL (Simple Encrypted Arithmetic Library), IBM's HElib, and PALISADE have become the de facto standards in the industry and form the basis for many commercial platforms. These libraries provide the fundamental building blocks. They include implementations of the most popular fully homomorphic encryption (FHE) schemes, such as BFV and BGV for integer arithmetic, and CKKS for approximate real-number arithmetic, which is particularly useful for machine learning applications. These libraries are highly complex to use directly. They require the developer to have a deep understanding of cryptographic parameters, such as the polynomial modulus and the noise budget of the ciphertext, which must be carefully managed to ensure both the correctness of the computation and the security of the data. The performance of this core library is a critical factor, and much of the ongoing research is focused on optimizing these low-level implementations to make homomorphic operations faster.
To make the technology more accessible, commercial platforms and advanced open-source projects build a high-level abstraction layer on top of the core library. This layer aims to hide the underlying cryptographic complexity from the developer. For example, instead of requiring the developer to manually manage the "noise" in a ciphertext, the platform might provide a compiler or a transpiler that can take a standard program written in a language like Python or C++ and automatically convert it into a homomorphic circuit that can be executed on encrypted data. Zama's Concrete library is a leading example of this approach, using a technique called "programmable bootstrapping" to allow for arbitrary functions to be run on encrypted data. This abstraction layer is the key to broadening adoption. It allows a data scientist to write a machine learning model using familiar tools like TensorFlow or PyTorch and have the platform automatically compile it to run on encrypted data, without them needing to become an expert cryptographer. This is a critical step in moving homomorphic encryption from a niche tool for cryptographers to a mainstream tool for all developers.
The final layer of the platform is the application and integration layer. This is where the homomorphic encryption capabilities are embedded into a specific business application or workflow. For a healthcare application, this might be a cloud-based service where a hospital can upload an encrypted patient genome and have a third-party AI model run a risk analysis on the encrypted data. The platform would need to include secure APIs for uploading the encrypted data and retrieving the encrypted result, as well as tools for managing user keys and access policies. In a financial services context, the platform might be used to build a secure multi-party computation service where several banks can jointly analyze their encrypted transaction data to detect fraudulent patterns without revealing their individual customer data to each other. These end-to-end applications are what deliver the final business value. They are often built by specialized startups or by the professional services divisions of large tech companies, using the underlying core libraries and abstraction layers to create a complete, privacy-preserving solution for a specific industry problem, thus completing the full platform stack.
Explore Our Latest Trending Reports:
- Art
- Causes
- Crafts
- Dance
- Drinks
- Film
- Fitness
- Food
- Games
- Gardening
- Health
- Home
- Literature
- Music
- Networking
- Other
- Party
- Religion
- Shopping
- Sports
- Theater
- Wellness


